Today I’m publishing a paper (PDF, arXiv) I wrote about the linkability of certain types of Zcash transactions. I’m also publishing a list of round-trip transactions generated as part of the research. The code used is up on GitHub (parser, database generator). If you don’t feel like reading the whole thing, there’s a summary below!
Note: A draft of the paper was shared with the Zcash Company before publishing. They have published a blog regarding the results.
As you probably know, Bitcoin is a “transparent ledger”, which means that it is very simple (and in fact, essential to verifying its correctness) to trace the flow of coins from one address to another. In this way, the transactions are “linkable”. Zcash is a fork of Bitcoin that adds in a new type of address called shielded addresses or a “z-addrs”. Transactions involving z-addrs use a special type of cryptography (zk-SNARKs) to obscure the parties and amounts of transactions.
The use of z-addrs is optional. Transparent addresses, or “t-addrs”, are essentially equivalent to Bitcoin transactions. Coins can be sent between z-addrs and t-addrs. However, when doing a mixed transaction (t→ z or z→ t) the amount of the transaction is public, even while the corresponding z-addr is not. Zcash has noted that this introduces the potential for linkability.
To begin, I looked into exactly how prevalent the use of z-addrs really is. I found that only 19.6% of transactions involve any use of a z-addr. Furthermore, 98.1% of these transactions performed either a t → z transaction or a z → t transaction. The conclusion is that the use of true private transactions (z → z) is fairly rare.
Coins that are controlled by z-addrs are said to be in the “shielded pool”. I found that this pool is relative shallow; on average only 3.5% of the available coins are in the shielded pool.
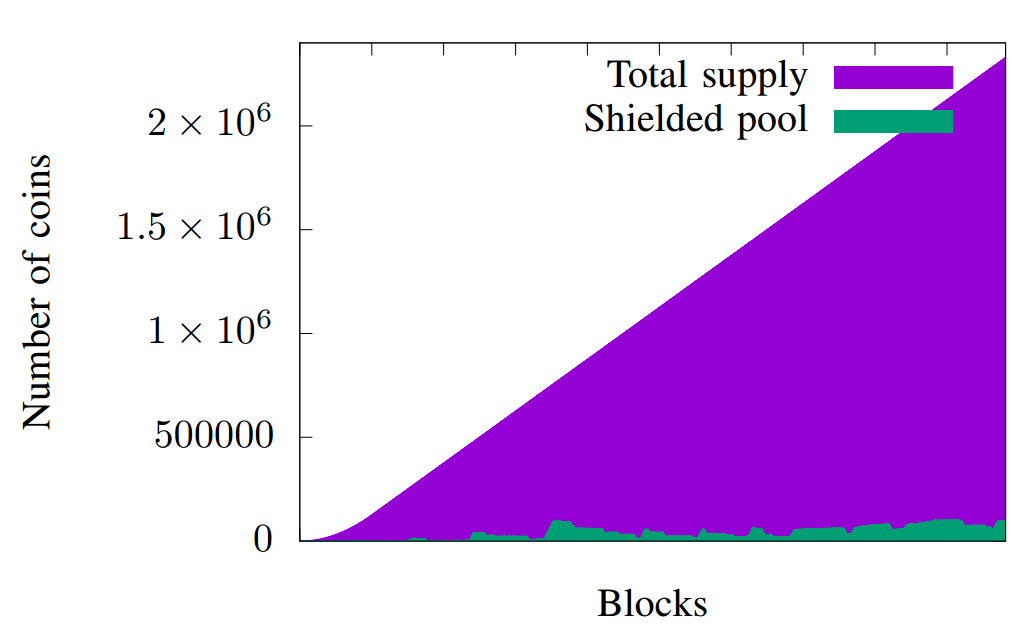
With 19.6% of transactions making use of z-addrs, an average of only 3.5% of coins in the shielded pool suggests that coins that enter the pool are soon sent back to t-addrs. Since the amounts of these types of transactions are public, we can look for pairs of transactions (t → z and then z → t) where the same number of coins are sent to the pool and then back to a t-addr. I called these transactions round-trip transactions.
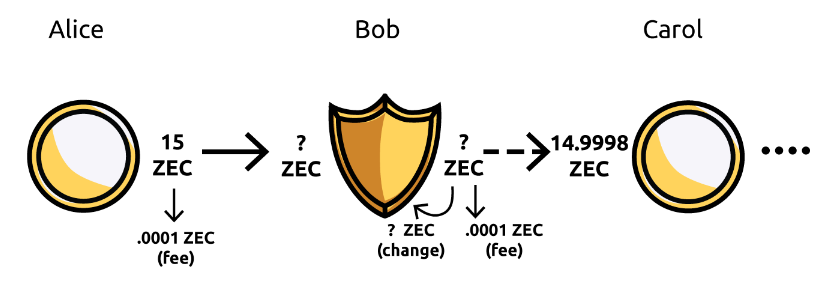
I searched the entire Zcash blockchain, looking for cases where t → z and z → t transactions had exactly the same number of coins transferred. To reduce false positives, I restricted the search to only those cases where the match was globally unique throughout the history of Zcash, e.g. if a t → z transaction was for 3.87514 ZEC, I looked if there was exactly one z → t transaction later on the blockchain for 3.87514 ZEC as well.
The motivation for this search was a suspicion that many people attempt to (for lack of a better word) launder their Zcash through the shielded pool. Since no exchanges or web wallets support z-addrs, users are forced to operate mainly through t-addrs if they want to use their coins. However, if they wish to obscure the source of these coins, they may pass them through the shielded pool. But, if they are not careful and make the amounts identical, the transaction may not be as private as they thought.
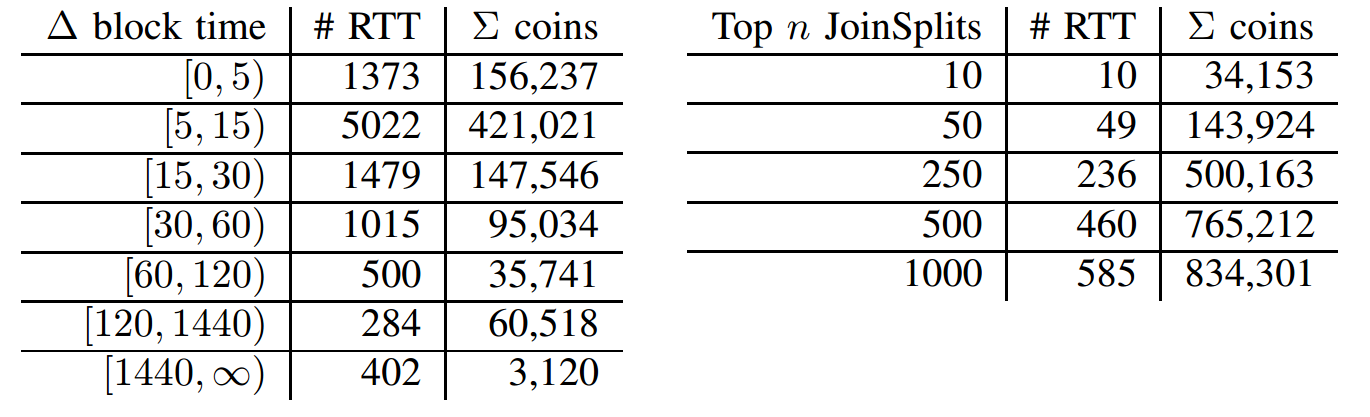
I was able to find 10,075 round-trip transactions (as of block 196304). 96% of these were between transactions that appeared within two hours of each other on the blockchain. This is strong circumstantial evidence that the transactions are linked. The transactions themselves are available here.
The RTTs surprisingly accounted for 31.5% of all coins that ever entered the shielded pool. In fact, 236 of the top 250 t → z transactions (by amount) were involved in a RTT. After investigating the addresses involved it appears many Zcash mining pools are engaging in RTTs before distributing their miner rewards. The members of the mining pool may be under the impression that the source of their coins is private, but their privacy is contingent on the sender of the coins having the foresight to not perform a RTT.
This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.